Expressvpn Glossary
DNS A record
What is a DNS A record?
DNS A is one of the most common types of Domain Name System (DNS) records. It maps a domain name or hostname to an IPv4 address, allowing a name like example.com to resolve to a numeric address like 93.184.216.34. These numeric addresses help computers find the correct host on an IP network.
DNS A records are stored as part of a DNS zone, which contains all DNS records for a particular domain or portion of the DNS namespace. In many setups, this data is managed in a zone file, though modern DNS systems do not always store it as a literal file. Authoritative DNS servers host the zone data and answer queries for the records they contain.
A single name can have multiple A records, each pointing to a different IPv4 address. When queried, DNS can return multiple addresses for that name, which can support simple traffic distribution and redundancy.
While A records store IPv4 addresses, DNS also supports AAAA records, which store IPv6 addresses.
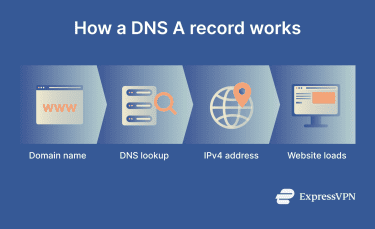
How does a DNS A record work?
When a device requests a domain name, a recursive resolver performs the lookup on the device's behalf:
- Initial query: A device sends a DNS request to a recursive resolver.
- DNS hierarchy lookup: If the resolver does not already have a cached answer, it typically follows the DNS hierarchy, starting with the root, then the top-level domain (TLD), and then the authoritative name server for the domain. In practice, many of these referrals are cached, so live root lookups are relatively uncommon.
- Answer: The authoritative server returns the A record with the domain’s IPv4 address, if one exists.
- Caching: The response includes a time to live (TTL) value that tells the resolver how long to store the record. This prevents the resolver from repeatedly querying authoritative servers for frequently requested domains. The resolver stores the A record and reuses it for repeat queries until the TTL expires.
Why is a DNS A record important?
DNS A records help websites and online services to load by translating domain names into IPv4 addresses that browsers and applications use to connect. Without this translation, clients cannot map a hostname to the correct IPv4 address, and the intended resource may be unreachable
A records must stay current when IPv4 addresses change. If a service moves to a new IPv4 address but the A record is not updated, DNS may continue returning the old address, which can prevent clients from reaching the intended service. Organizations may use static IP addresses, dynamic DNS updates, or intermediaries such as load balancers and content delivery networks (CDNs) to help keep services reachable when infrastructure changes.
Missing or misconfigured A records can break access. Without a valid IPv4 address in the DNS response, hostname resolution cannot return the address needed for an IPv4 connection.
DNS A record vulnerabilities
Cybercriminals can exploit DNS misconfigurations and weaknesses in DNS resolution to redirect traffic, expose information, or compromise trust in a domain.
- DNS spoofing: Attackers send false DNS responses that redirect users from legitimate websites to malicious ones. This can happen on compromised networks or through man-in-the-middle attacks (MITMs). DNS System Security Extensions (DNSSEC) was designed to help protect against this kind of tampering.
- DNS cache poisoning: Attackers inject false information into a DNS resolver’s cache, causing it to return incorrect IP addresses and direct users to destinations under the attacker's control.
- Subdomain takeover: When an organization stops using a third-party service but leaves the DNS A record pointing to it, attackers may be able to claim the abandoned resource and serve content from that subdomain. This risk is especially associated with dangling Canonical Name (CNAME) records, though other dangling DNS or delegation setups can also create similar problems.
- Query metadata exposure: DNS queries reveal both the requested domain name and the source IP address to parties that can observe the lookup path. When DNS traffic is unencrypted, this can allow internet service providers (ISPs), network administrators, or attackers on the network to monitor which domains a user looks up and associate those queries with a device or network connection.
Further reading
- DNS record types explained: A complete guide for privacy
- What is DNS, and how does it work? The Domain Name System explained simply
- Types of DNS servers and how they work
- DNS security: How to protect your network from DNS threats


