Expressvpn Glossary
Data exfiltration
What is data exfiltration?
Data exfiltration is the unauthorized and covert transfer of data from a system, network, or device to an external destination. It typically involves sensitive information such as personal data, financial records, intellectual property, or confidential business documents.
How data exfiltration occurs
Data exfiltration typically occurs through either external intrusion or internal activity.
In an external attack, an unauthorized party infiltrates the network from the outside, accesses corporate or user data, and transfers it outside the organization’s control.
Internal activity involves individuals who have already authorized access to systems. An insider may intentionally remove data for personal gain or share it without authorization. In other cases, employees expose sensitive information through negligence or improper handling.
Common data exfiltration attack techniques
These techniques enable attackers to gain access to systems or sensitive data before exfiltration occurs.
- Social engineering and phishing: Attackers deceive individuals into revealing credentials or granting access to systems. This often involves fraudulent emails, messages, or websites designed to appear legitimate.
- Credential compromise: Stolen or reused passwords allow attackers to access systems with legitimate user privileges.
- Vulnerability exploitation: Attackers exploit unpatched software flaws or system weaknesses to gain unauthorized access.
- Malware deployment: Malicious software establishes persistence within a system and enables attackers to access or collect sensitive data.
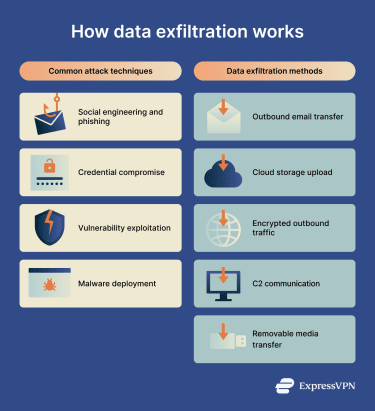
Common data exfiltration methods
Once access has been established, attackers use specific methods to transfer data outside the organization.
- Outbound email transfer: Sensitive information is sent to external email accounts as attachments or embedded content.
- Cloud storage upload: Files are uploaded to unauthorized cloud storage or file-sharing services.
- Encrypted outbound traffic: Data is transmitted through encrypted network channels like HTTPS, which uses Transport Layer Security (TLS), or through Domain Name System (DNS)-based communication to avoid detection.
- Command-and-control (C2) communication: Compromised systems send collected data to external servers controlled by attackers.
- Removable media transfer: Data is copied to physical storage devices, such as USB drives, and removed from the organization.
Risks, privacy, and compliance implications of data exfiltration
Data exfiltration exposes organizations and individuals to significant risk. Unauthorized removal of sensitive information can lead to financial loss, operational disruption, and reputational harm. Stolen data may enable fraud, identity theft, intellectual property misuse, or competitive exploitation.
When exfiltration involves regulated data, organizations may face legal and compliance obligations. Failure to address unauthorized data transfers may result in penalties, legal exposure, and regulatory scrutiny.
There are also certain conditions that increase exfiltration risk, such as:
- Extended dwell time: Longer undetected access allows attackers to escalate privileges and extract larger volumes of data.
- Over-permissioned accounts: Excessive access rights expand the amount of data available for extraction.
- Encrypted outbound traffic: Encrypted channels can conceal unauthorized transfers from basic monitoring systems.
- Third-party integrations: Misconfigured external applications create additional pathways for data removal.
Further reading
- What is SSL inspection in network security?
- DNS security: How to protect your network from DNS threats
- The ultimate guide to recursive DNS: Everything you need to know
- Zero-trust data protection explained
- Security concerns in cloud computing and how to address them
- What is Secure Access Service Edge (SASE)?


